protected!
A Federal judge in Vermont ruled today that a defendant can’t be compelled to reveal the password used to decrypt files on his or her hard drive. From the ruling:
Compelling Boucher to produce the password compels him to display the contents of his mind to incriminate himself…The foregone conclusion doctrine does not apply to the production of non-physical evidence, existing only in a suspect’s mind where the act of production can be used against him.
This is good news for electronic privacy. Unfortunately, there is already precedent allowing law enforcement to install a key logger on a suspect’s computer to obtain the encryption password without the suspect’s knowledge. So I guess this ruling (for as long as it stands) just protects us when law enforcement wasn’t smart enough to install a key logger before charging us with a crime and seizing our computers.
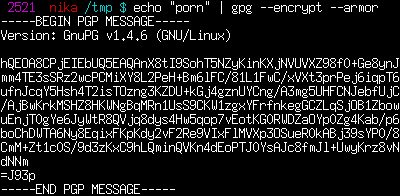
I wonder what, if any, case law exists to compel a person to reveal the code used to encrypt a hand-written diary? Do we have more privacy rights now that our PGP/GPG keys are part of our fifth amendment right not to act as a witness against ourselves?
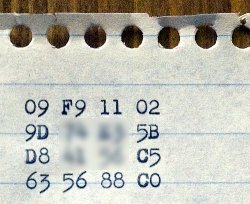
image by 500cpm, blurred by me
Apparently one of the encryption keys for the high definition DVD (HD-DVD) format has been discovered, and is now appearing and disappearing all over the Internets. The organization in charge of “administering” the encryption scheme has started sending out Digital Millennium Copyright Act (DMCA) takedown notices to Internet Service Providers and corporations whenever they find the key on a website. Here’s one such notice sent to Google. The incredibly stupid part about this document is that it contains the key they’re trying to hide in the letter, officially putting it in the public record.
The whole thing is ridiculous. If I buy an HD-DVD disc, I’m not allowed to make a copy of it in case my copy gets scratched or broken because doing so would require “breaking” the encryption which is a violation of the DMCA. The key is part of this process, so the content corporations are trying with all their might (and their lawyers in concert with the DMCA) to keep the key a secret so that people can’t make backups of the items they have purchased.
But you can’t take back a secret once it’s out. And even if you could, it’s ridiculous that it’s possible to shut down a web site because it contains a simple string of letters and numbers that by themselves mean absolutely nothing. Or a photograph of something that happens to contain the string (click on the image for a whole set of these from Flickr). The string isn’t copyrighted, and it’s not a trademark. It seems like free speech means I ought to be able to print this string of letters and numbers.
[Update: There's a great legal discussion of the issues at the Electronic Freedom Foundation's web site. The link is 09 f9: A Legal Primer. The gist is that putting the key on the Internet serves no other purpose than to aid in circumventing protected content, and thus, posters can be sued for “trafficking.”]
Here’s the secret key, which I’ve converted to bits and then encrypted: 00010011 11110010 00100010 00000101 00111010 11101001 11000110 10110111 10110000 10000010 10101101 10001010 11000110 10101101 00010001 10000000. Is this a violation of the DMCA? It’s not actually the key and thus is useless to someone who wants to exercise their right to make a backup of something they’ve purchased because I’ve “encrypted” it (does x << 1 mean anything to you?). Because I’ve encrypted it, does that give me protection under the DMCA? If I get a takedown notice, that implies that the laywer sending the letter has circumvented the access controls to my copyrighted data (because this post is Copyrighted, and so the bitstring is too).
When will this insanity end?